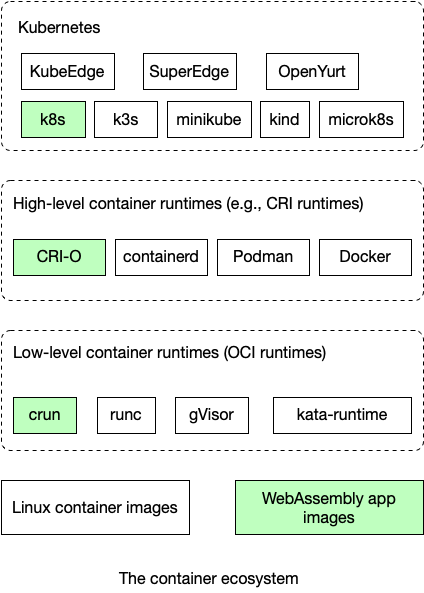
Developers can leverage container tools such as Kubernetes, Docker and CRI-O to deploy, manage, and run lightweight WebAssembly applications. In this article, we will demonstrate how Kubernetes ecosystem tools work with WasmEdge WebAssembly applications.
Compared with Docker, WebAssembly could be 100x faster at startup, have a much smaller memory and disk footprint, and have a better-defined safety sandbox. However, the trade-off is that WebAssembly requires its own language SDKs, and compiler toolchains, making it a more constrained developer environment than Docker. WebAssembly is increasingly used in Edge Computing scenarios where it is difficult to deploy Docker containers or when the application performance is vital.
One of the great advantages of application containers like Docker is the rich ecosystem of tools. The good news is that you can use the exact same tools to manage WebAssembly applications, enabling Docker-like Linux containers and WebAssembly apps to run side-by-side in the same system.
A demo app
The demo application is a Rust app compiled into WebAssembly bytecode, and then packaged and published as an OS-less container image on Docker Hub. We will then use container tools to start and run this WebAssembly app image.
See instructions on how to build and publish this WebAssembly app image.
Low-level container runtime
The container image can be started by any OCI-compliant container runtime, such as crun. The crun project has WasmEdge support baked in. Use the commands below to build and install a crun executable binary with WasmEdge support on Ubuntu.
git clone https://github.com/containers/crun
cd crun
./autogen.sh
./configure --with-wasmedge
make
sudo make install
High-level container runtime
The high-level container runetime, such as CRI-O, pulls container images from registries (e.g., Docker Hub), manages them on disk, and launches a lower-level runtime to run container processes.
CRI-O: Check out the instructions on how to use CRI-O with crun to pull, start, and manage the WebAssembly app image.
Kubernetes
Most high-level container runtimes implement Kubernetes’ CRI (Container Runtime Interface) spec so that they can be managed by Kubernetes tools. That means you can use Kubernetes tools to manage the WebAssembly app image in pods and namespaces.
Kubernetes: Check out the instructions on how to create and run pods for the WebAssembly app image.
What's next
In this article, we have seen how to pull, start, run, and manage WasmEdge applications using container tools. Our ongoing effort is to support as many container runtimes and Kubernetes frameworks as possible to run Linux containers and WebAssembly app containers side-by-side.
Join us in the WebAssembly revolution!
👉 Slack Channel: #wasmedge on CNCF Slack channel
👉 Mailing list: Send an email to WasmEdge@googlegroups.com
👉 Be a contributor: Check out our wish list to start contributing!
👉 Twitter: WasmEdge
